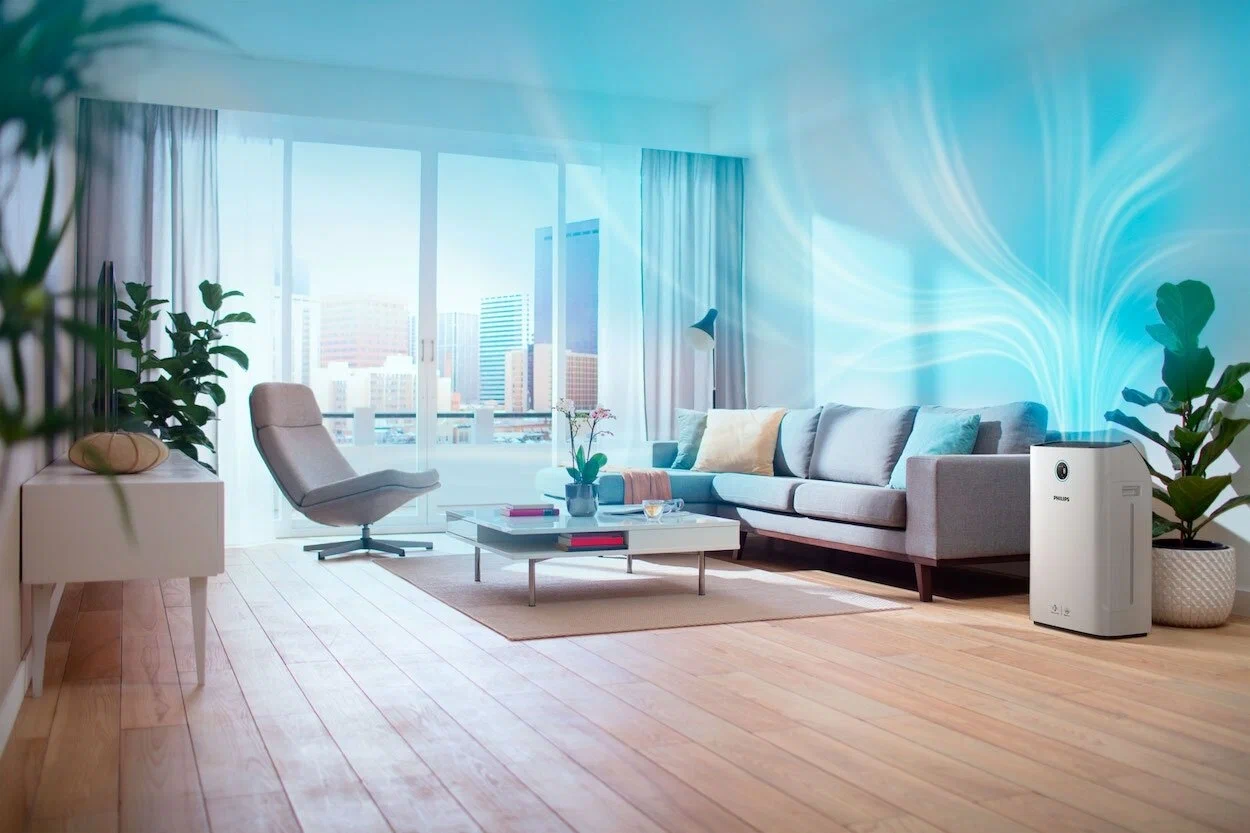
Transforming Spaces, One Breath at a Time
Our real-time air quality monitors, EC fans, and electronic filtration systems work together to deliver the purest air possible
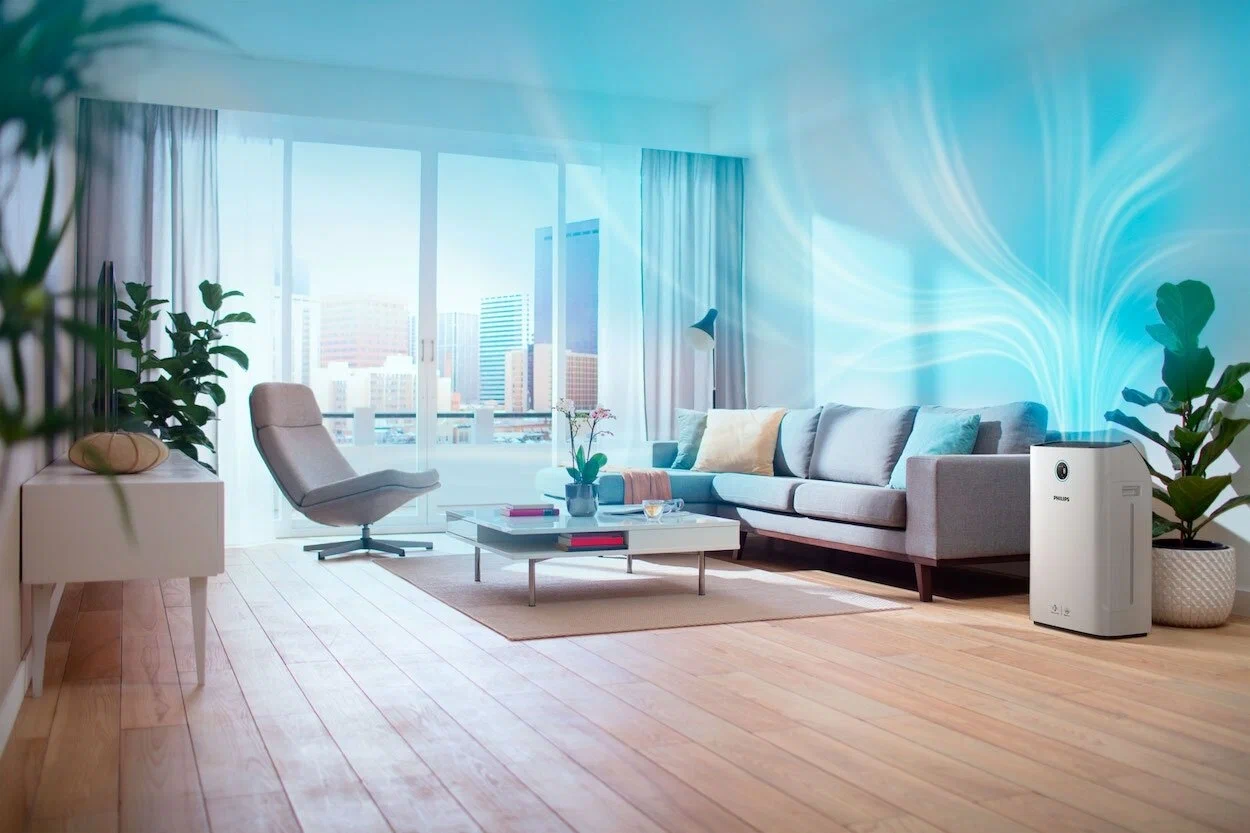
Our real-time air quality monitors, EC fans, and electronic filtration systems work together to deliver the purest air possible


Our real-time air quality monitors, EC fans, and electronic filtration systems work together to deliver the purest air possible
Our WELL-compliant monitors deliver highly accurate sensor readings, feature Wi-Fi connectivity, and boast a sleek glass finish that complements any interior
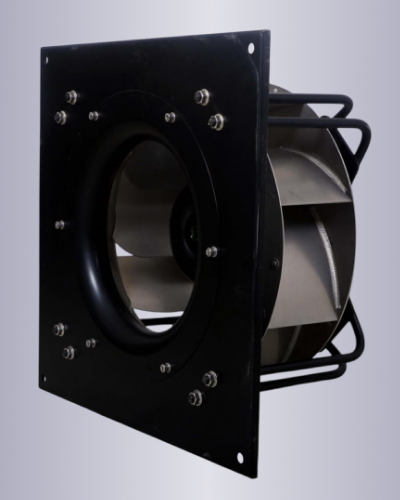
Our best in class high efficiency, high performance EC fans are ideal for purified air ventilation

Our WELL Compliant sensors are best in class and provide the needed accuracy to get any project certified

Market Leading efficiency with minimal heat emissions and perform well even at partial loads

Our monitors allow for demand control ventilation making the overall system very energy efficient while maximizing occupant comfort

Our Wi-fi enabled AQI monitors are tightly integrated with our EC fans, providing unparalleled hardware software integration, resulting in best in class performance.
A , colloquially referred to as Visualizer 3D OKM Keygen 21 , attempts to meet that need. The “21” suffix designates the second‑generation, version 2.1, of the visualizer, which introduced a host of performance and usability improvements over its predecessor. This essay surveys the motivations behind such a tool, its architectural foundations, the way it renders cryptographic processes in three dimensions, and the broader implications for education, auditing, and future security tooling. 2. Why Visualize Key Generation? | Traditional View | What a 3‑D Visualizer Adds | |----------------------|--------------------------------| | Opaque – the algorithm is a line of code that produces a byte string. | Concrete Geometry – each step of the KDF, entropy pool, and PRF is mapped to a visual node, enabling users to see how randomness propagates. | | Static Audits – auditors rely on logs and code review. | Dynamic Exploration – auditors can pause, rewind, or zoom into the moment where entropy is consumed, catching subtle implementation flaws. | | Educational Gap – students learn theory but rarely witness practical execution. | Intuitive Learning – 3‑D metaphors (e.g., swirling particle clouds for entropy, gears for hash functions) translate abstract math into tangible experience. | | Limited Debugging – developers must add verbose logging. | Live Debugging – the visualizer surfaces bottlenecks (e.g., low entropy sources) instantly, reducing time‑to‑fix. |
1. Introduction In modern security engineering, the generation of cryptographic keys is often treated as a “black‑box” operation: a deterministic algorithm consumes entropy and outputs a secret value, while the surrounding software merely stores or transports the result. As systems grow in complexity and as security audits become more stringent, a new need has emerged – visual transparency . visualizer 3d okm keygen 21
As security systems continue to evolve—embracing quantum‑resistant primitives, distributed key management, and increasingly complex entropy sources—tools that make the inner workings of these systems visible will become indispensable. The 3‑D visualizer is a concrete step in that direction, turning abstract mathematics into an observable, interactive, and ultimately more trustworthy reality. A , colloquially referred to as Visualizer 3D
"Ready to improve your indoor air quality? Get in touch with us today to explore our certified IAQ solutions. Breathe easier, live healthier—contact us now!"
A , colloquially referred to as Visualizer 3D OKM Keygen 21 , attempts to meet that need. The “21” suffix designates the second‑generation, version 2.1, of the visualizer, which introduced a host of performance and usability improvements over its predecessor. This essay surveys the motivations behind such a tool, its architectural foundations, the way it renders cryptographic processes in three dimensions, and the broader implications for education, auditing, and future security tooling. 2. Why Visualize Key Generation? | Traditional View | What a 3‑D Visualizer Adds | |----------------------|--------------------------------| | Opaque – the algorithm is a line of code that produces a byte string. | Concrete Geometry – each step of the KDF, entropy pool, and PRF is mapped to a visual node, enabling users to see how randomness propagates. | | Static Audits – auditors rely on logs and code review. | Dynamic Exploration – auditors can pause, rewind, or zoom into the moment where entropy is consumed, catching subtle implementation flaws. | | Educational Gap – students learn theory but rarely witness practical execution. | Intuitive Learning – 3‑D metaphors (e.g., swirling particle clouds for entropy, gears for hash functions) translate abstract math into tangible experience. | | Limited Debugging – developers must add verbose logging. | Live Debugging – the visualizer surfaces bottlenecks (e.g., low entropy sources) instantly, reducing time‑to‑fix. |
1. Introduction In modern security engineering, the generation of cryptographic keys is often treated as a “black‑box” operation: a deterministic algorithm consumes entropy and outputs a secret value, while the surrounding software merely stores or transports the result. As systems grow in complexity and as security audits become more stringent, a new need has emerged – visual transparency .
As security systems continue to evolve—embracing quantum‑resistant primitives, distributed key management, and increasingly complex entropy sources—tools that make the inner workings of these systems visible will become indispensable. The 3‑D visualizer is a concrete step in that direction, turning abstract mathematics into an observable, interactive, and ultimately more trustworthy reality.